Penggemar Touring? Berikut 5 Destinasi Wisata yang Cocok – Wacana soal kendaraan sepeda motor yang diusulkan bisa masuk ke jalan tol kini tengah hangat menjadi perbincangan. Hal tersebut kini menuai pro dan kontra, ada yang menyetujui hal tersebut namun tak sedikit pula yang menolak wacana tersebut karena memang seharusnya motor tidak boleh masuk ke dalam jalan tol karena pertimbangan keamanan.
Terlepas dari hal tersebut, mari kita lupakan sejenak perdebatan mengenai wacana motor yang akan diperbolehkan memasuki jalan tol. Karena, tahu kah kamu? Ternyata ada banyak destinasi wisata menarik yang letaknya tidak jauh dari Jakarta dan dapat kamu kunjungi sembari touring dengan menggunakan sepeda motor, lho. sbobet365
Nah di mana sajakah tempat tersebut? Berikut lima destinasi yang asyik untuk touring dengan menggunakan sepeda motor yang berhasil dirangkum. judi bola
1. Gunung
Pancar
Destinasi pertama yang asik untuk touring dengan menggunakan sepeda motor adalah Gunung Pancar. Gunung yang terletak di daerah Sentul, Bogor, Jawa Barat ini juga berada tidak jauh dari Jakarta sehingga sangat mudah untuk menuju ke sana. https://americandreamdrivein.com/
Menawarkan
keindahan alam dan pesona pegunungan yang masih asri, tempat ini sangat tepat
buatmu yang ingin menghilangkan penat dari segala rutinitas yang ada dan juga
hiruk-pikuk kota.
Udara yang
segar dengan hamparan hutan pinusnya yang hijau, pasti akan membuatmu ingin
berlama-lama di sana. Tak hanya itu, di Gunung Pancar juga terdapat banyak spot
foto dengan latar belakang pegunungan yang indah.
Jika Anda
mau rehat sejenak dari kehidupan hiruk pikuk bisingnya perkotaan, Gunung Pancar
dapat menjadi salah satu alternatif wisata bagi Anda. Berikut adalah beberapa
hal yang dapat Anda lakukan di objek wisata ini.
– Berburu
foto instagenik di hutan pinus
Konsep alam
dan natural ala Huta Pinus dapat anda jadikan tema untuk mengisi laman sosial
media anda. Untuk dapat berfoto di kawasan ini, Anda perlu membayar sekitar
Rp20.000. Tak terlalu mahal jika dibandingkan dengan panorama yang akan anda
dapatkan.
– Lakukan
kegiatan olahraga agar tubuh tetap bugar
Jogging di
kawasan ini dapat menjadi tantangan sekaligus kesenangan tersendiri. Pasalnya,
jalur jogging yang ada memang tak semulus trek jogging di pusat olahraga maupun
stadion. Namun, dengan udara yang begitu segar, jalur jogging di kawasan ini
dapat menjadi pilihan.
– Pemandian
air hangat di tengah dinginnya pegunungan
Di tengah
pepohonan pinus yang menjulang tinggi, di kawasan wisata Gunung Pancar juga
terdapat pemandian air panas yang siap meredakan lelah Anda. Sepuluh menit anda
berendam di pemandian air panas, rasa pegal, dan lelah pun berangsur hilang.
Otot yang kaku pun kembali rileks.
– Terapi,
aktivitas luar ruangan, hingga glamping
Di sekitar
kawasan pemandian air hangat Tirta Sanita, Anda dapat menemukan berbagai macam
terapi yang akan membuat tubuh Anda semakin bugar. Beberapa di antaranya yakni
terapi ikan, terapi bekam, terapi lintah, kolam untuk permainan air, juga
paket-paket aktivitas luar ruangan (outbond) untuk dewasa ataupun anak-anak.
– Wisata
budaya di Kaki Gunung Pancar
Selain itu,
di kawasan Gunung Pancar ini anda dapat berziarah ke makam keramat yang ada. Di
puncaknya, anda dapat melihat makam-makam keramat yang telah ada sejak zaman
dahulu
– Cocok
untuk resepsi pernikahan tema Rustic
Beberapa
orang mengartikan rustic wedding sebagai konsep pernikahan dengan gaya pedesaan
yang elok, berkaitan dengan alam dan sederhana. Konsepnya yang menawarkan
suasana asri dan alami meninggalkan sensasi dan kenangan tersendiri. Salah satu
lokasi outdoor wedding yang populer yakni di wilayah hutan pinus. Masyarakat
mulai beramai ramai mengadopsi konsep pernikahan ala Bella Swan dan Edward
Cullen di film Twilight.
2. Taman
Nasional Gunung Salak
Selain
Gunung Pancar, tempat selanjutnya yang juga asyik untuk kamu datangi sembari
touring adalah Taman Nasional Gunung Halimun Salak (TNGS). Masih berada di
daerah Bogor, di TNGHS dapat dijangkau hanya dengan beberapa jam saja dari
Jakarta.
Saat sampai
di kawasan TNGHS terdapat sekitar tujuh curug yang dapat dikunjungi para
wisatawan, beberapa di antaranya adalah Curug Cigamea, Curug Pangeran, Curug
Ngumpet, Curug Seribu dan curug lainnya.
Akan tetapi,
curug yang ramai dikunjungi wisatawan adalah Curug Cigamea. Tiket masuk setiap
curug juga berbeda-beda, jadi sebaiknya kamu membawa uang lebih ya jika ingin
mengunjungi beberapa curug sekaligus.
Di tempat
ini, panorama alam khas pegunungan yang disuguhkan juga tidak akan
mengecewakanmu, ditambah udara yang segar akan membuatmu betah berlama-lama di
sana.
3. Geopark
Ciletuh- Pelabuhan Ratu
Tak hanya di
Bogor, Sukabumi juga memiliki beberapa destinasi wisata yang asik untuk kamu
jelajahi dengan menggunakan sepeda motor.
Tempat
tersebut antara lain Geopark Ciletuh yang terletak di Sukabumi, Jawa Barat.
Kawasan ini
meliputi 74 desa dalam 8 kecamatan. Karena sangat luas, tentu geopark ini tak
cukup dijelajahi dalam sehari. Apalagi
Geopark Ciletuh sendiri dibagi menjadi tiga area, yakni Geoarea Ciletuh, Geoarea
Simpenan, Geoarea Cisolok. Menariknya lagi, di sini tersebar 50 objek wisata
yang bisa kamu nikmati di sana.
Untuk menuju
Geopark Ciletuh kamu membutuhkan waktu setidaknya sekitar 5-6 jam.
4. Ujung
Genteng
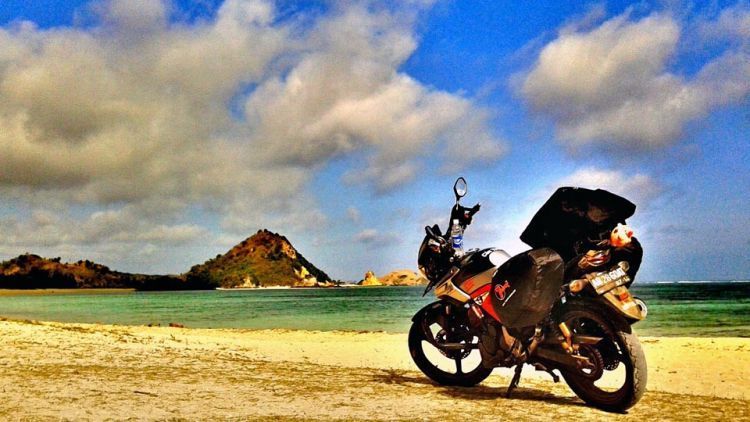
Masih berada
di daerah Sukabumi, Ujung Genteng adalah tempat berikutnya yang dapat kamu
kunjungi dengan menggunakan sepeda motor. Saat menuju tempat ini kamu akan
disuguhkan dengan panorama alam yang indah dan juga bentang alam yang asri
dengan udara sejuk khas pegunungan.
Pantai ini
dikenal dengan suasana pantainya yang sepi dan tenang karena letaknya yang jauh
dari keramaian. Sehingga sangat tepat bagi wisatawan yang menyukai ketenangan
dan kedamaian.
Bicara soal
pantai, pantai di kawasan ini sanggup memukau wisatawan dengan pasir putihnya
yang memanjakan mata. Kamu juga tak akan menyesal menghabiskan liburan di sana,
pasalnya, sepanjang perjalanan menuju Pantai Ujung Genteng pun kamu sudah
disuguhi hijaunya pemandangan yang indah karena melewati pegunungan yang
berkelok-kelok.
5. Pantai
Sawarna
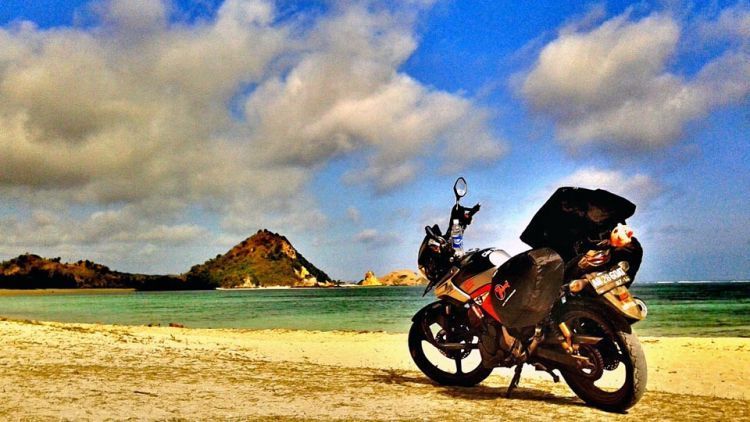
Tempat
selanjutnya yang menarik untuk kamu kunjungi adalah Sawarna. Terletak di daerah
Banten, Sawarna dikenal memiliki pantai yang indah yang menjadi destinasi
favorit wisatawan.
Tempat
wisata ini dikenal memiliki pantai-pantai indah yang memukau wisatawan. Selain
pemandangannya yang indah, Pantai Sawarna juga memiliki salah satu gua yang
bernama Gua Lalay yang dikenal cukup indah dan tujuh pantai dengan panorama
alam yang berbeda-beda tentunya sangat sayang untuk kamu lewatkan.
Berdasarkan
peta Pantai Sawarna menghadap ke Samudera Hindia. Dikarenakan letaknya yang
menghadap ke Samudera Hindia inilah yang membuat pantai Sawarna memiliki ombak
yang besar dengan arusnya yang kuat. Biarpun letak pantai Sawarna terpencil dan
akses untuk menuju ke pantai ini cukup sulit dijangkau, tidak lantas membuat
pengunjung menyerah. Mereka masih mau berkunjung ke wisata ini. Karena
keindahan pantai ini Sawarna laksana surga yang tersembunyi di wilayah
terpencil.
Dikarenakan
deburan ombaknya yang dahsyat, tak jarang banyak pengunjung baik wisatawan
domestik maupun mancanegara yang ingin berselancar di pantai ini. Dan ya,
karang yang terdapat di ujung lautan bisa Anda jadikan spot untuk
berselfie-selfie ria bersama teman-teman.